Improve system,
network & data
security
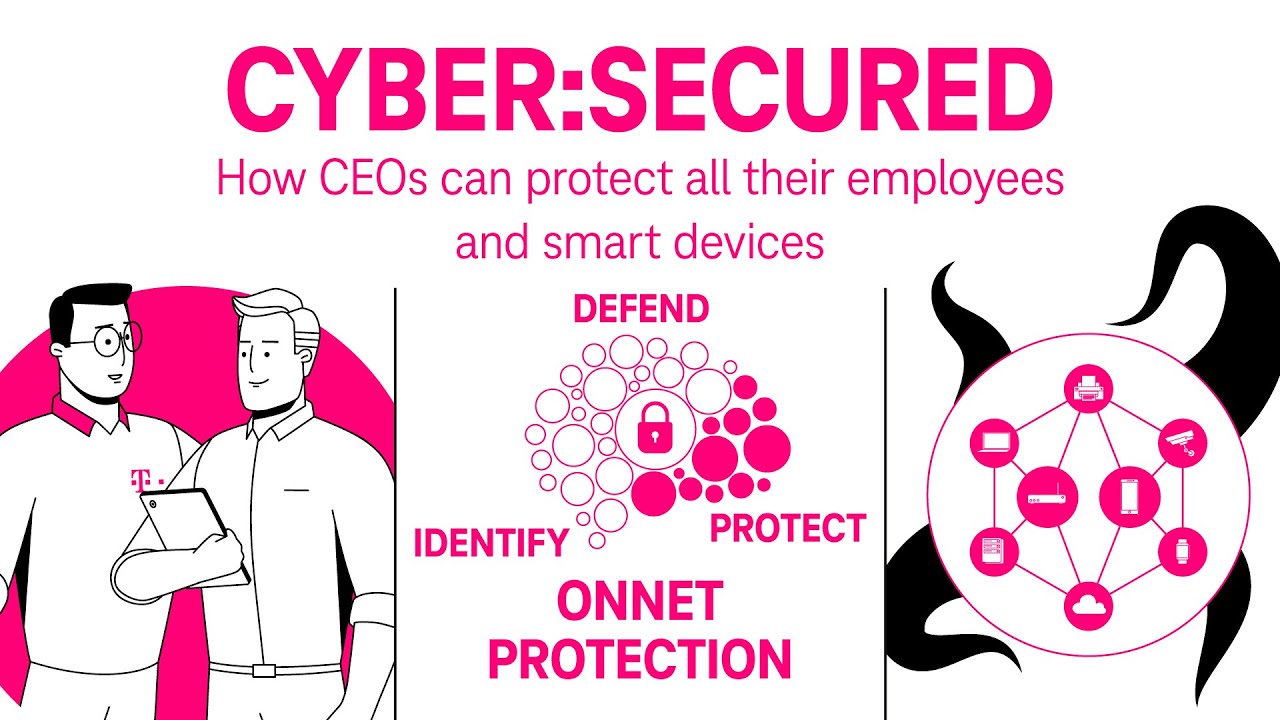
Efficient strategies for network, system, and data security start by applying measures to keep attackers out and away from your operations. We help you do exactly that with our Identify-Protect-Defend model.
Your digital workplace and communication is essential to keep your business running. We help you protect your environment from external threats by securing internal and external interconnection points. What’s more, we also show you how to increase your data security by securing your processes and training your staff in IT security so they can act as a first line of defense. Your competitive advantage is also vital to how you do business, and you need to protect it from both exposure and loss. That’s why we examine your network flow to build the right foundations to protect your digital workplaces, email accounts, and sensitive data and secure your networks to keep cybercriminals out.
Increase your
data security
Keep your infrastructure safe and protect it from external threats by securing internal and external interconnection points. We also increase your data security efficiently with IT security training courses.
Cyber:Secured—How CEOs can protect their company
Learn more about how Telekom Business can help you protect both your employees and IoT devices.
How do we secure your
data, systems, and networks?
A successful security strategy keeps hackers out. Our solutions secure your data, systems, processes, networks, and endpoints to ensure your business is perfectly safe.
1. Secure processes

Security Policies
We manage unique Information Technology (IT) security policies to help you set rules and procedures for everyone who accesses and uses an organization’s IT assets and resources. The aim is to preserve the confidentiality, integrity, and availability of systems and information used by an organization’s members. The policies should detail objectives, scope, specific goals, and responsibilities for compliance as well as the actions to be taken in the event of non-compliance.

Security Awareness
We address, mitigate, reduce, and even eliminate risk, loss, and threats with targeted awareness training. This helps create a workplace environment that enhances productivity and contributes to the bottom line by preventing attacks. The aim here is to transform a risk-averse, reactive security management culture into a proactive, results-based model.

Table Top Exercises
What if an incident occurs? Before it comes to that, we help you improve your overall cyber response posture and collective decision-making process. We do this by taking participants through a simulated incident scenario and providing hands-on training designed to highlight any flaws in incident response planning (responsibilities, roles, authorities, resources, etc.).

Red Teaming
Red Team Assessment is designed to meet the needs of complex organizations handling a variety of sensitive assets either in technical, physical, or process terms. Red teaming aims to demonstrate how real-world attackers can combine seemingly unrelated exploits to achieve their goals. Because instead of relying on a single network appliance or system to secure sensitive data, it’s much better to adopt a Defense in Depth (DiD) approach and continuously improve your people, processes, and technology.

Cybersecurity Insurance
This service includes both hardware insurance (e.g. replacing a broken phone) and cyber insurance to help mitigate losses from a variety of cyber incidents. Our goal is to help protect your organization from cybercrime and digital threats, which is why we offer a range of cyber insurance products – from specialist, standalone cyber insurance to dedicated cyber risk cover.
2. Secure networks

Managed Web Application Firewall
A web application firewall (WAF) protects web applications from a variety of application layer attacks, such as SQL injection and cookie poisoning, among others. Attacks on apps are the leading cause of breaches as they’re the perfect gateway to your valuable data. However, with the right WAF in place, you can prevent a huge array of attacks that aim to exfiltrate data by compromising your systems.

Unified Threat Management
Unified Threat Management (UTM) is an approach to information security in which a single hardware or software installation provides multiple security functions. Instead of several single-function appliances all requiring training, attention, and support, network administrators can instead manage their security centrally from a single computer. This naturally makes it much easier to increase data security.

Intrusion Prevention System
An Intrusion Prevention System (IPS) is a network security/threat prevention technology that examines network traffic flows to detect and prevent vulnerability exploits.
Any intrusion activity or violation is reported either to an administrator or collected using a Security Information and Event Management (SIEM) system which combines outputs from multiple sources and uses alarm filtering techniques to distinguish malicious activity from false alarms.
Anti DDoS
A denial-of-service attack (DoS attack) aims to make a machine or network resource unavailable to its intended users. In a Distributed Denial-of-Service attack (DDoS attack), the incoming traffic flooding the victim originates from many different sources making it impossible to stop the attack simply by blocking a single source. However, our solutions help you fight these threats effectively.

On-net Protection
On-net security is a network-based solution that enables service providers and carriers to take full advantage of their existing infrastructure by providing fully converged security with a mass-market approach. We help you secure your work with web browsers and protect your network at all levels by blocking known malicious sites containing viruses, scams, etc.

Virtual Private Network
Our VPN as a service is a robust, cost-effective solution that allows employees outside your company to connect to company resources securely and reliably. We provide our VPN as a service so that companies don’t have to invest in their own tools and can simply rely on a proven solution instead.
3. Secure systems

Increase email security
Email security protects email accounts, content, and communication from unauthorized access, loss, and compromise. Our solutions not only protect you from malware, spam, and phishing attacks but also cybercriminals using deceptive messages to entice recipients to part with sensitive information, open attachments, or click on hyperlinks that install malware on the victim’s device.

Advanced Threat Protection
Stop threats before they reach your staff and respond quickly when things go wrong. Our innovative Advanced Threat Protection solutions prevent, detect, and notify you of advanced threats – via email, mobile, social, and desktop – and help you resolve them before they cause lasting harm.

Boost cloud security
Around 70% percent of CEE companies already use cloud services on account of the business opportunities offered by cloud-based infrastructure. But they often pay far too little attention to a very important topic: data security. We help you ensure that your company is using any and all cloud computing technology safely.
Cloud Web Gateway
Cloud web gateways are security policy enforcement points that sit between cloud service consumers and cloud service providers. They can be either on-premise or cloud-based and allow enterprise security policies to be enforced whenever cloud-based resources are accessed. Example security policies include authentication, single sign-on, authorization, security token mapping, encryption, tokenization, logging, alerting, API control, and so on.
4. Secure endpoints

End-point Protection
We help you protect your organization by using password management tools and much more. Enjoy end-point protection with next-generation anti-virus solutions and contemporary tools for Wi-Fi protection, managing passwords, and more.

Mobile Device Management
An effective Mobile Device Management (MDM) platform helps your IT and Security departments manage all your organization’s devices – regardless of their type or operating system. It provides the perfect support to keep your devices secure and your workforce flexible and productive.
5. Secure data

Data Loss Prevention
Data loss prevention (DLP) software detects and prevents potential data breaches and data exfiltration by monitoring, detecting, and blocking sensitive data while in use (endpoint actions), in motion (network traffic), and at rest (data storage).

Identity Access Management
Identity and access management (IAM) is a framework of business processes, policies, and technologies that makes it easy to manage electronic and digital identities. Your IT managers can use it to control access to critical information within your organization by employing single sign-on systems, two-factor/multifactor authentication, and privileged access management.

Cloud Access Security Broker
A cloud access security broker (CASB) is a security policy enforcement point that sits between cloud service consumers and cloud service providers. It can be either on-premises or cloud-based and allows enterprise security policies to be combined and enforced whenever cloud-based resources are accessed. You can think of a CASB as a sheriff enforcing the laws laid down by cloud service administrators (source: Gartner).
Related
content
Would you like to learn more about this topic in your country?
Go directly to the relevant for your country and learn more about our local product portfolio.
Select country

Our experts are more than happy to
answer any questions you might have.